Geek Stuff 0
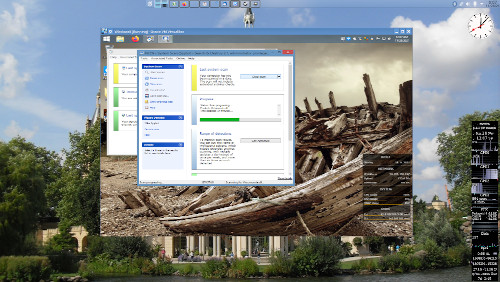
Running Spybot S & D in a VirtualBox virtual machine of Windows 8 on Ubuntu MATE with the Plasma desktop environment.
If you use Windows, you really should be using Spybot. It protects you from many variants of spyware.

Virginia Beach
Second Thursday of the Month
Drinking Liberally Website
Join us at Meetup.
Follow the conversation at Facebook.
In the latest migration to a new virtual private server, some of the links to images in the earliest posts to this blog were broken. If you encounter one of these broken links, please let me know. I have backups and can restore the images.


There’s only one person who agrees with me on everything, and, as I’m not running for office, that person is not on the ballot.


Running Spybot S & D in a VirtualBox virtual machine of Windows 8 on Ubuntu MATE with the Plasma desktop environment.
If you use Windows, you really should be using Spybot. It protects you from many variants of spyware.